You've invested in firewalls, endpoint protection, and
cybersecurity training. But here's the uncomfortable truth: all of that can be
undone by a single unlocked door.
Your network closet, that small, often-overlooked room
housing your critical IT equipment, could be your biggest security
vulnerability. And if you're like most business owners, you're not thinking
about it until it's too late.
At GDS Technology, we understand that managed IT services
mean protecting every aspect of your infrastructure, including the physical
spaces where your hardware lives. Let's talk about why your network closet
demands the same attention as your digital defenses, and what happens when it
doesn't get it.
What Is the Network Closet and Its Role in Cybersecurity?
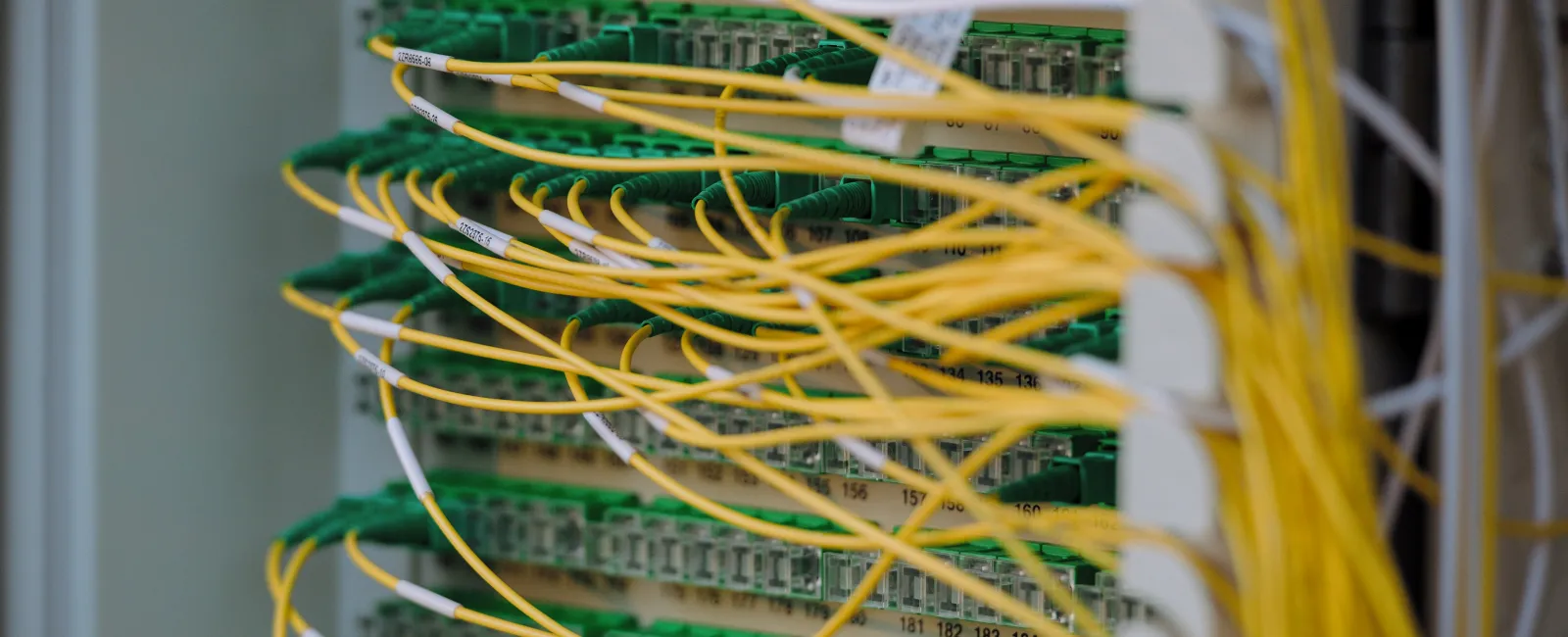
Your network closet is the center of your IT infrastructure,
housing the switches, routers, servers, firewalls, and more that keep your
business connected and operational. What makes this space so vulnerable is that
anyone with physical access can bypass virtually every digital security measure
you've implemented.
Anyone can install devices to capture sensitive data, create
backdoors into your network, or disconnect equipment to bring operations to a
halt.
According to IBM's
2024 Cost of a Data Breach Report, nearly 1 in 10 data breaches stem from
physical security compromises. That's staggering when you consider how much
businesses spend on digital security.
The Dangerous Oversights Made by Businesses
Most businesses are shocked when we point out the glaring
vulnerabilities in their network closet security.
Lack of Physical Security
- Unlocked doors
- Network closets in shared spaces
- Keys distributed without tracking
- No surveillance cameras or protective barriers
Inadequate Monitoring
- Little to no monitoring
- No cameras, access logs, or environmental sensors
- No alerts if something goes wrong.
Outdated Hardware
- Switches installed years ago
- Outdated firmware
- Network equipment that hasn't been updated
Lack of Training or Supervision
- Lack of team training
- Third-party vendor access
- New employees
- Human error
Real-World Risks of Ignoring Network Closet Security
Let's move beyond theory and talk about what actually
happens when network closet security fails.
The Coca-Cola Incident
In 2014, equipment was stolen from Coca-Cola's largest
bottling plant, compromising sensitive employee information, including health
data and financial details. The breach stemmed from inadequate physical
security, precisely the kind of oversight that network closet vulnerabilities
create.
The Cost of Disruption
According to IBM's 2024 Cost of a Data Breach Report, the
global average cost of a data breach has reached $4.88 million, a 10% increase
from the previous year. But the financial impact is only part of the story.
It takes organizations an average of 204 days to identify a
breach and another 73 days to contain it. That's nearly nine months of
exposure. Breaches that extend beyond 200 days cost an average of $5.46
million.
This is on top of the operational disruptions, downtime,
reputational damage, legal liabilities, and regulatory fines that come from
such an incident.
How We Can Help Secure Your Network Closet
This is where managed IT services make all the
difference.
At GDS Technology, we don't just react to problems, we
prevent them. Here's how we approach network closet security as part of our
comprehensive cybersecurity services:
Vulnerability Assessment
We conduct thorough assessments covering physical security, equipment inventory, firmware status, cable management, environmental controls, and access documentation. Many businesses don't even know what equipment they have in their network closets, let alone whether it's secure.
Regular Audits and Maintenance
Through our managed IT services, we verify that all
equipment is up to date with security patches, review access logs for unusual
activity, test backup power systems, inspect physical security measures, and
update documentation as equipment changes.
Staff Training
We work with your entire team to ensure everyone understands
proper access procedures, contractor and vendor guidelines, emergency response
protocols, and regular security awareness updates.
Comprehensive Cybersecurity Strategy
We integrate physical security with your broader
cybersecurity framework, including network segmentation, intrusion detection
systems, regular security testing, and disaster recovery planning that
accounts for both digital and physical threats.
The Importance of Integrating Network Closet Security into Your
Cybersecurity Plan
Your business cybersecurity solutions are only as
strong as your weakest link. When we evaluate your security through our
Business Optimization Process, we examine every layer: perimeter security,
physical security, network security, endpoint security, application security,
and data security. Protecting your network closet is critical to this
comprehensive approach.
Many cybersecurity policies focus exclusively on digital
threats. We help you update policies to include procedures for network closet
access, protocols for equipment changes, emergency response plans for security
breaches, and regular training.
If your industry requires compliance with HIPAA, PCI DSS, or
CMMC, network closet security is vital. We ensure your network closet
vulnerabilities meet or exceed compliance requirements, protecting you from
regulatory penalties.
Stop Putting Your Business at Risk
You wouldn't leave your front door unlocked at night. So why
leave your network closet accessible to anyone who walks by?
The reality is that most businesses overlook network closet
security until it's too late. They focus on firewalls and antivirus software but
ignore physical access points, which can cost millions in breach costs, lost
business, and damaged reputation.
At GDS Technology, we take a different approach. We
understand that true managed IT services mean protecting every aspect of
your infrastructure. Our proven Business Optimization Process ensures that protecting
your network closet isn't an afterthought, it's a fundamental part of your
security strategy.
Don't wait for a breach to expose your vulnerabilities. Take
action now to secure your network closet and your business from cyber attacks.
Click Here or give us a call at 404-719-5222 to Book a FREE 15-Minute Discovery Call